News
Microsoft Turning on Azure Active Directory Publisher Verification Next Month
Microsoft plans to turn on a new Azure Active Directory "Publisher Verification" security feature that will block end user consent to unverified app publishers starting next month.
Unverified apps will get blocked after Nov. 8, 2020, per a Wednesday Microsoft announcement. The Publisher Verification scheme was developed to address so-called "consent phishing," where apps registered via OAuth 2.0 providers, including Azure AD, are used to gain excessive permissions. These permissions might include access to a user's "mail, forwarding rules, files, contacts, notes, profile and other sensitive data and resources," a July Microsoft post on consent phishing explained.
Microsoft's own applications sometimes request such permissions in order to work. It seems that attackers have been leveraging that sort of approval routine to gain a foothold.
The Publisher Verification scheme is for so-called "multitenant" or hosted applications that integrate with the Microsoft Identity Platform, or that use OAuth 2.0 and OpenID Connect authentication methods. App publishers need to be part of the Microsoft Partner Network and go through an app verification process to avoid scenarios where end users won't be able to give consent. The deadline is next month.
The Publisher Verification scheme isn't a Microsoft certification program. Microsoft doesn't charge anything for apps to get verified. More details are described in this Microsoft "Publisher Verification" document.
Blue Badges
Apps that come from verified publishers will be notable by having blue badge icons. End users will see these icons within an Azure AD consent dialog box when asked to grant permissions to an app.
An example of the blue badge icon can be seen below:
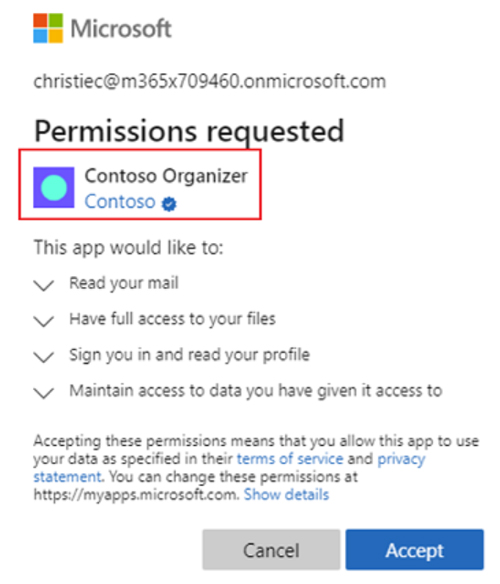 Blue badge icon in permissions dialog box indicating an app publisher was verified. (Source: Microsoft "Publisher Verification" document)
Blue badge icon in permissions dialog box indicating an app publisher was verified. (Source: Microsoft "Publisher Verification" document)
Consent Policies
The Publisher Verification scheme was at the preview stage back in May, but it reached "general availability" commercial-release status last month. Also at general availability now is the ability of IT pros to set app consent policies.
IT pros can set app consent policies to disable the ability of end users to grant permissions to apps. Alternatively, IT pros can allow users to grant consent to verified publishers and apps registered within the organization's tenancy, which seems to be Microsoft's recommended approach.
It's also possible to set custom policies on granting consent. These policies can be set using "Azure AD PowerShell or Microsoft Graph," per the announcement.
About the Author
Kurt Mackie is senior news producer for 1105 Media's Converge360 group.