Posey's Tips & Tricks
Creating Policy Configurations for Office 365 Users
For decades, group policies have been the go-to mechanism for securing devices on a Windows network. The problem with using group policies, however, is that they generally require a device to be domain-joined (with local security policies being the notable exception). In this day of BYOD, one cannot simply assume that users will only be working from domain-joined devices.
Thankfully, Microsoft allows Office 365 admins to implement group policy-like controls through Office policy configurations.
Before I show you how to create an Office policy configuration, there are some things that you need to know. First, Office policy configurations are different from group policies. Group policies are divided into user settings and device settings. Office policy configurations only apply to users, not devices.
Another thing you need to know is that in order for the policies to be applied, users must be signed into Azure Active Directory and running version 1808 or higher of Office 365 ProPlus.
To get started, go to the Office 365 Client Configuration Service page and sign in using an administrative account. When you log in, you are taken to the Office Customization Tool. If you are not familiar with the Office Customization Tool, I recommend taking the time to explore its various options. The Office Customization Tool can help you create a file that can be used to perform automated Office 365 ProPlus deployments that match your organization's specifications. You can see what the Office Customization Tool looks like in Figure 1.
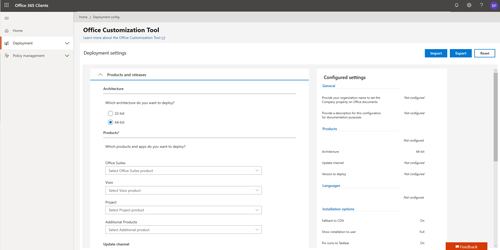 [Click on image for larger view.] Figure 1: This is what the Office Customization Tool looks like.
[Click on image for larger view.] Figure 1: This is what the Office Customization Tool looks like.
Since the ultimate goal is to create a policy configuration (rather than to perform a custom deployment), click on the Policy Management tab. When you do, the tab will expand to reveal the presence of a Policy Configuration sub-tab. Click on the Policy Configuration tab to access the Policy Configurations page.
At this point, you will likely see a message indicating that you do not yet have any policy configurations. Go ahead and click on the Create button, shown in Figure 2, to create your first policy configuration.
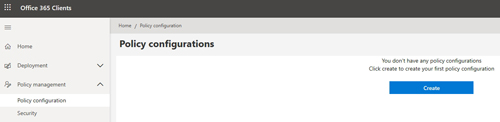 [Click on image for larger view.] Figure 2: Click on the Create button to create a policy configuration.
[Click on image for larger view.] Figure 2: Click on the Create button to create a policy configuration.
You will now be taken to the Create Policy Configuration screen, which you can see in Figure 3. The first step in creating a policy configuration is to enter a name for the policy configuration that you are creating. There is also a field where you can enter a detailed description of the policy configuration. Even so, I recommend using a good, descriptive name. Over time you may accumulate multiple policy configurations, and so it is helpful to use a naming scheme that helps you differentiate between policy configurations.
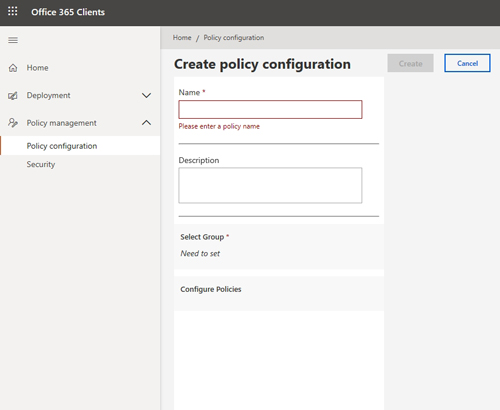 Figure 3: This is what the Create Policy Configuration screen looks like.
Figure 3: This is what the Create Policy Configuration screen looks like.
Once you have entered a name and description for the policy configuration, the next step is to select a group to which you wish to bind the policy. It is worth noting that each policy configuration can only be bound to one group, and a group can only have one policy configuration associated with it. Keep in mind that a user could potentially belong to more than one group, which could result in policies being applied to that user in an unexpected way.
Once you have selected a group, then the next step in the process is to configure the actual policy settings. This can end up being a big job because there are currently over 1,300 individual policy settings that you can configure. Furthermore, I would not be a bit surprised if Microsoft introduced additional policy settings in the future.
As you can see in Figure 4, all of the policy settings are initially set to Not Configured. If you want to configure a particular policy setting, just click on it and then select whatever configuration option you deem to be appropriate for your organization.
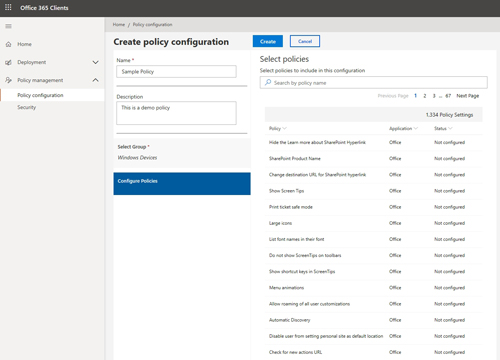 [Click on image for larger view.] Figure 4: There are currently over 1,300 individual policy settings available for use.
[Click on image for larger view.] Figure 4: There are currently over 1,300 individual policy settings available for use.
Once you finish configuring any policy settings that you want to apply to group members, just click on the Create button to create the policy configuration.
About the Author
Brien Posey is a 22-time Microsoft MVP with decades of IT experience. As a freelance writer, Posey has written thousands of articles and contributed to several dozen books on a wide variety of IT topics. Prior to going freelance, Posey was a CIO for a national chain of hospitals and health care facilities. He has also served as a network administrator for some of the country's largest insurance companies and for the Department of Defense at Fort Knox. In addition to his continued work in IT, Posey has spent the last several years actively training as a commercial scientist-astronaut candidate in preparation to fly on a mission to study polar mesospheric clouds from space. You can follow his spaceflight training on his Web site.