Posey's Tips & Tricks
Microsoft Finally Lets Windows Defender Protect Itself
A recently added "tamper protection" feature finally corrects an obvious security gap in Microsoft's anti-malware solution.
Over the years, I have developed something of a love/hate relationship with Windows Defender. On one hand, Windows Defender has actually caught malware infections that other anti-virus programs have missed. It certainly hasn't happened very often, but it has happened.
The best example I can think of is an incident that occurred way back in 2015. Windows Defender discovered a virus within an old file that was stored on my file server. While it might not seem all that remarkable that an anti-malware tool discovered a malware infection, there were two things that made this incident noteworthy. First, that server's contents had been scanned many times before by other anti-malware tools. Second, this particular infection had evaded detection for 17 years! According to my server logs, that particular file had not been accessed since the 1990s.
I was so taken aback by the discovery that I actually mentioned it on Facebook (my Facebook account is only used for communicating with close friends and family, and I never post anything technical):
The point is that on at least a couple of occasions, Windows Defender managed to do something really awesome.
On the other hand, though, I have seen Windows Defender fail far more times over the years than I have seen it succeed. I couldn't even begin to guess how many times I have had friends or family ask me to take a look at a malware infection, and in most of those cases Windows Defender (or its predecessor, Microsoft Security Essentials) had been disabled by the malware.
The idea that Windows Defender could be disabled and that critical system files could be tampered with by malware never sat well with me. I always speculated that it would be relatively easy for the Windows operating system to ensure the integrity of its own code (there are various mechanisms in place to do that now) and for Microsoft to treat Windows Defender as a core OS service that cannot be disabled.
Thankfully, Microsoft finally seems to be taking Windows Defender seriously.
To see what I mean, take a look at Figure 2. I arrived at this screen by going to Settings and then clicking on Update and Security, followed by Windows Security.
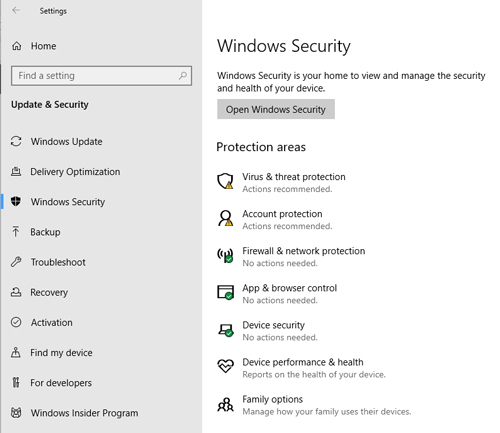 [Click on image for larger view.] Figure 2: There are virus and threat protection related actions being recommended.
[Click on image for larger view.] Figure 2: There are virus and threat protection related actions being recommended.
As you can see in the figure, the Virus and Threat Protection section indicates that there are some actions that are recommended. Clicking on this text causes Windows to display the Virus and Threat Protection screen, which you can see in Figure 3.
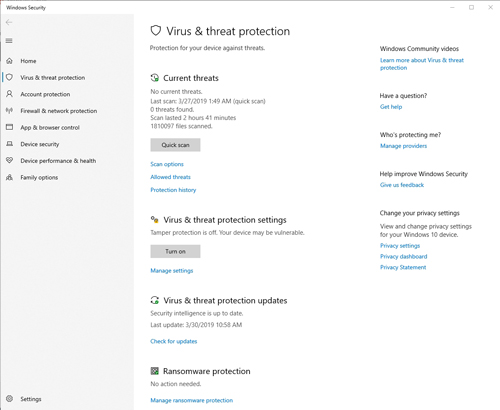 [Click on image for larger view.] Figure 3: You can manage Windows Defender through the Virus and Threat Protection screen.
[Click on image for larger view.] Figure 3: You can manage Windows Defender through the Virus and Threat Protection screen.
As you can see in the figure above, Microsoft has recently introduced a tamper-protection feature for Windows Defender. This feature prevents malware from being able to turn off Windows Defender protection. The reason why Windows indicated that actions were recommended (as evidenced by the warning icon in the figure above) is because tamper protection is currently turned off.
I applaud Microsoft for introducing tamper protection for Windows Defender. At the same time, though, I'm not quite sure why Microsoft requires tamper protection to be manually enabled. That requirement would seem to violate Microsoft's secure-by-default initiatives.
As you saw in Figure 3, enabling tamper protection is a simple matter: Just click the Turn On button and tamper protection will be enabled. Once you have done that, the screen will change to indicate that no action is needed. You can see what this looks like in Figure 4.
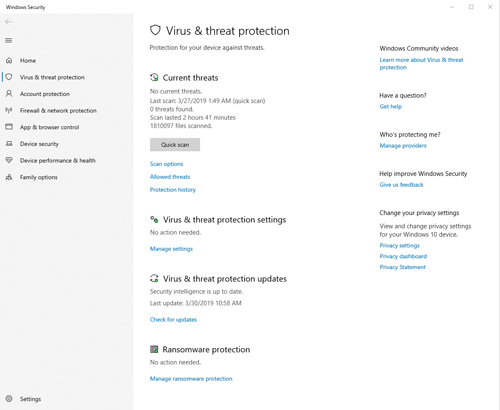 [Click on image for larger view.] Figure 4: This is what you will see after tamper protection has been enabled.
[Click on image for larger view.] Figure 4: This is what you will see after tamper protection has been enabled.
So, is Windows Defender good enough to replace a commercial anti-malware solution? I honestly don't know. It has been years since I have done any head-to-head testing.
My own experiences have been that Windows Defender does a decent job of detecting malware infections, but only if the infection does not disable it before it has a chance to take action. My guess is that the new tamper-protection feature will go a long way toward keeping your system safe from malware.
About the Author
Brien Posey is a 22-time Microsoft MVP with decades of IT experience. As a freelance writer, Posey has written thousands of articles and contributed to several dozen books on a wide variety of IT topics. Prior to going freelance, Posey was a CIO for a national chain of hospitals and health care facilities. He has also served as a network administrator for some of the country's largest insurance companies and for the Department of Defense at Fort Knox. In addition to his continued work in IT, Posey has spent the last several years actively training as a commercial scientist-astronaut candidate in preparation to fly on a mission to study polar mesospheric clouds from space. You can follow his spaceflight training on his Web site.