'Rapid Cyberattacks' the Most Novel Security Threat To Emerge in 2017?
The massive Equifax breach dominated the security headlines last year, but Microsoft security experts are contending that Petya and WannaCrypt are representative of a dangerous new category of cyberattacks that emerged in force in 2017.
In a blog post Tuesday, Mark Simos, lead cybersecurity architect for the Microsoft Enterprise Cybersecurity Group, said the two attacks "reset our expectations" for how bad a cyberattack can be in terms of speed and scope of damage. Simos termed Petya and WannaCrypt, also known as WannaCry, as "rapid cyberattacks."
As a definition for this class of attacks, Simos wrote, "Rapid cyberattacks are fast, automated, and disruptive -- setting them apart from the targeted data theft attacks and various commodity attacks, including commodity ransomware, that security programs typically encounter."
To fit the bill, an attack must be rapid, spreading in minutes through an enterprise; automated, with no human interaction required; and disruptive, with intentional destruction or encryption of data and systems.
Both pieces of malware exploited vulnerabilities in Windows. Petya first appeared in early 2016 as a somewhat standard family of encrypting ransomware that encrypted hard drives, then prompted users for a Bitcoin payment.
The novel bits came in June 2017 in a severe cyberattack with worldwide effect, but that hit Ukraine especially hard and prompted suspicion that it was a targeted assault on that country's infrastructure. The Petya variant used in that case, also called NotPetya, spread through compromised tax preparation software common in Ukraine called MEDoc. NotPetya also used the EternalBlue exploit of a Windows Server Message Block vulnerability and other techniques to traverse networks. EternalBlue had been leaked by the Shadow Brokers hacker group in April 2017, and was widely believed to be a U.S. National Security Agency (NSA) hacking tool. Additionally, NotPetya encrypted the file system but solely to destroy a computer; there were no ransom requests.
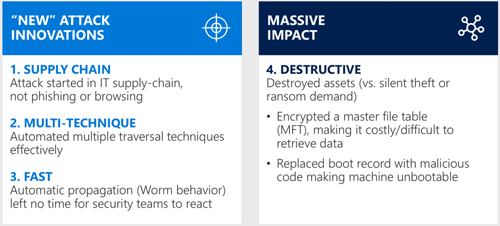 [Click on image for larger view.] Petya broke from typical security attacks in four ways. (Source: Mark Simos/Microsoft)
[Click on image for larger view.] Petya broke from typical security attacks in four ways. (Source: Mark Simos/Microsoft)
WannaCry/WannaCrypt, which also spread via EternalBlue without user interaction, also did some severe and widespread damage for a few days in May before a security researcher accidentally discovered a kill switch.
Focusing on Petya, Simos said that particular rapid cyberattack surprised defenders in four ways. It used the supply chain to enter target environments via the MEDoc application instead of phishing or browsing. Petya employed multiple propagation techniques. The malware moved across networks very quickly, outpacing defenders' ability to detect and respond to the attack. Finally, the lack of an apparent ransom motive made the malware destructive.
Simos and Jim Moeller, principal consultant for Cyber Security at Microsoft, address the issues in an on-demand webinar called "Protect Against Rapid Cyberattacks (Petya [aka NotPetya], WannaCrypt, and similar)."
Posted by Scott Bekker on 01/24/2018