Windows Server How-To
How To Fix Windows Server Network Performance Problems
If your server network performance is lagging, chances are Windows' security features are to blame. Here's how to alleviate the problem.
One of the problems that has long plagued Windows Server 2012 (and now Windows Server 2012 R2) is extremely poor network performance. This problem doesn't occur on every Windows Server deployment, but there is no shortage of Windows Server 2012 and 2012 R2 servers that are impacted by the problem.
I first began to notice the problem shortly after the initial Windows Server 2012 release. Writing large files to SMB network shares was painfully slow. The file copy activity seemed to occur in bursts. The write process would start out at the expected speed, but after several seconds the transfer speed would drop to zero. Sometimes Windows would eventually begin copying data again, but timeouts were a big problem. All too often the file copy process would simply fail.
Needless to say, slow and potentially unreliable network traffic is a problem that absolutely must be addressed. Some have reportedly been able to fix this particular problem by switching to a different brand of network adapter. However, it is also possible to fix the problem by making some changes to your Group Policy settings.
More often than not, the network performance problems are the result of a Windows security feature. By default, Windows Server 2012 and 2012 R2 digitally sign SMB packets. This digital signature helps to protect against spoofing, but it adds some overhead to the traffic stream. You can get rid of this overhead and improve performance by disabling the SMB packet signing feature. Keep in mind however, that disabling SMB signing does reduce security, so you should only use this fix if you are experiencing disruptive performance or reliability problems.
To disable SMB signing for the computers on your domain, log into a Windows Server 2012 or 2012 R2 domain controller and then enter the GPMC.MSC command at the server's Run prompt. This will cause Windows to open the Group Policy Management Console.
Now, right-click on the Default Domain Policy and select the Edit command from the resulting shortcut menu, as shown in Figure 1.
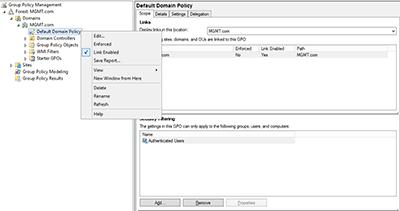 [Click on image for larger view.] Figure 1. Right-click on the Default Domain Policy and choose the Edit command from the shortcut menu.
[Click on image for larger view.] Figure 1. Right-click on the Default Domain Policy and choose the Edit command from the shortcut menu.
Now, navigate through the Group Policy Management Editor to Computer Configuration | Policies | Windows Settings | Security Settings | Local Policies | Security Options, as shown in Figure 2.
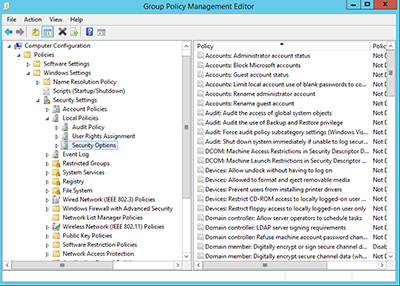 [Click on image for larger view.] Figure 2. The settings that you will need to modify are located in the Security Options container.
[Click on image for larger view.] Figure 2. The settings that you will need to modify are located in the Security Options container.
Now, disable the Microsoft Network Server: Digitally Sign Communications (Always) policy, as shown in Figure 3. You will also need to disable the Domain Member: Digitally Encrypt or Sign Secure Channel Data (Always) policy.
 [Click on image for larger view.] Figure 3. Disable the Microsoft Network Server: Digitally Sign Communications (Always) policy.
[Click on image for larger view.] Figure 3. Disable the Microsoft Network Server: Digitally Sign Communications (Always) policy.
Keep in mind that there will probably be additional group policies that need to be modified. At the very least, you will probably have to modify the Domain Controller Security Policy. You may also have to modify any other security policies that you are using.
So how much of a difference does this fix actually make? To find out, I copied a 2GB file, both before and after the fix.
If you look at Figure 4 below, you can see that prior to the fix, there were some really significant dips and spikes in the copy process. Although the graph does not do a very good job of illustrating it, there was a substantial amount of time during which the throughput was a steady zero bytes. It took four minutes and 11 seconds to copy a 2GB file. Personally, I am surprised that the file copied that quickly. I have definitely witnessed worse performance.
 [Click on image for larger view.] Figure 4. It took four minutes and eleven seconds to copy a 2GB file.
[Click on image for larger view.] Figure 4. It took four minutes and eleven seconds to copy a 2GB file.
The screen capture shown in Figure 5 below was taken after the fix had been put into place and the Group Policy settings had plenty of time to replicate. As you can see in the figure, the file copy operation was much more linear. Furthermore, the amount of time required to copy the file dropped from over four minutes to a mere 24 seconds!
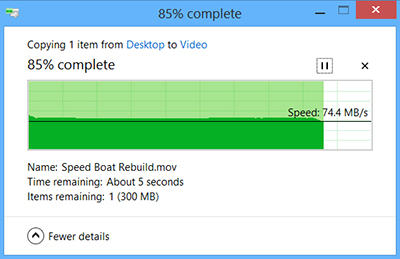 [Click on image for larger view.] Figure 5. The file copy process completed in 24 seconds!
[Click on image for larger view.] Figure 5. The file copy process completed in 24 seconds!
Again, you probably shouldn't disable SMB signing unless you are having performance or reliability problems. If you are having problems however, disabling SMB signing can make a huge difference.
About the Author
Brien Posey is a 22-time Microsoft MVP with decades of IT experience. As a freelance writer, Posey has written thousands of articles and contributed to several dozen books on a wide variety of IT topics. Prior to going freelance, Posey was a CIO for a national chain of hospitals and health care facilities. He has also served as a network administrator for some of the country's largest insurance companies and for the Department of Defense at Fort Knox. In addition to his continued work in IT, Posey has spent the last several years actively training as a commercial scientist-astronaut candidate in preparation to fly on a mission to study polar mesospheric clouds from space. You can follow his spaceflight training on his Web site.