Windows Server How-To
Running PowerShell's Best Practices Analyzer
Use PowerShell's baked-in analyzer to set up best practice scans.
Microsoft provides Best Practices Analyzer scans for a number of Windows components. What you might not realize however, is that it is easily possible to run the Best Practices Analyzer through Windows PowerShell. Doing so has a number of advantages. First, using PowerShell gives you a way of running the Best Practices Analyzer on Windows servers that are configured to operate without a GUI. Another advantage is that using PowerShell frees you from having to go searching through the graphical interface for the analyzer that you want to run. Furthermore, with a little bit of scripting, you can build a comprehensive best practices report.
Believe it or not, there are only four cmdlets that are specifically designed for use with the Best Practices Analyzer. Even so, these four cmdlets give you everything that you need to launch best practices scans. In this article, I am going to demonstrate the three most important cmdlets.
The first cmdlet that you need to know about is the Get-BpaModel cmdlet. This cmdlet queries the system to determine which Best Practices Analyzer modules are installed. You can see what this looks like in Figure 1.
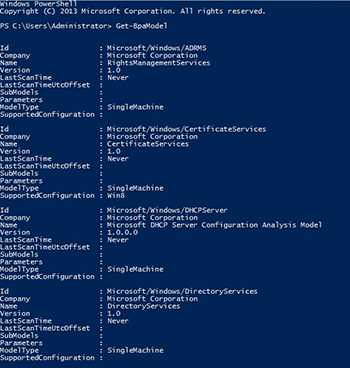 [Click on image for larger view.] Figure 1. You can use the Get-BpaModel cmdlet to find out which Best Practices Analyzer modules are installed on the system.
[Click on image for larger view.] Figure 1. You can use the Get-BpaModel cmdlet to find out which Best Practices Analyzer modules are installed on the system.
As you can see in the figure, there are typically quite a few modules installed on a server. The Get-BpaModel cmdlet actually shows you the last time a scan was performed using a given module.
The next cmdlet that you need to know about is Invoke-BpaModel, This cmdlet us used to launch a best practices scan. When you use this cmdlet, you will have to supply the model ID for the best practices module that you want to use. If you look at the previous figure, you can see that every Best Practices Analyzer model has an ID listed. To invoke a model you simply specify the –ModelID parameter, followed by the ID of the model that you want to use. For example, if you wanted to start a scan using the Hyper-V model then the command for doing so would be:
Invoke-BpaModel –ModelId Microsoft/Windows/Hyper-V
When you invoke a Best Practices Analyzer scan, PowerShell may appear to lock up while the scan is being run. When the scan is complete, you will see a few basic pieces of information about the scan displayed, as shown in Figure 2.
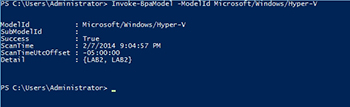 [Click on image for larger view.] Figure 2. This is what it looks like when you run a Best Practices Analyzer scan from PowerShell.
[Click on image for larger view.] Figure 2. This is what it looks like when you run a Best Practices Analyzer scan from PowerShell.
As you can see in the figure above, PowerShell confirms that the scan was successful, and it shows you which model was used and when the scan was run (as well as the time zone). The results even tell you which computer the scan was run on. What you don't see are the scan results. For that you will have to use the Get-BpaResult cmdlet.
This cmdlet is designed to retrieve the most recent scan results. You will however, have to specify the model ID for which you want to retrieve the results. For example, if you wanted to retrieve the results of the Hyper-V best practices scan that I performed in Figure 2, then the command for doing so would be:
Get-BpaResult –ModelID Microsoft/Windows/Hyper-V
You can see what the results look like in Figure 3.
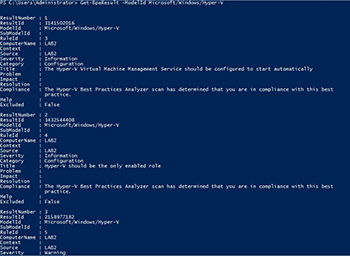 [Click on image for larger view.] Figure 3. The Get-BpaResult cmdlet retrieves scan results.
[Click on image for larger view.] Figure 3. The Get-BpaResult cmdlet retrieves scan results.
The problem with retrieving the result is that there is typically far more data than will fit on the screen. If you look at the figure above, you will notice that there are a number of lines of text for each result, and for this scan there were 71 results. That being the case, we need a way to either narrow down the results or export them to a file, or both.
One way to narrow down the results is by severity. To show you what I mean, suppose that you only wanted to display the scan results for which the severity is listed as error. We can also configure PowerShell to only display some of the more useful information about each error. A command for doing so might look like this:
Get-BpaResult –ModelId Microsoft/Windows/Hyper-V | Where-Object {$_.Severity –eq 'Error'} | FL Title, Problem, Resolution, Help
As you can see in Figure 4, this command's output is much more helpful than what was originally displayed.
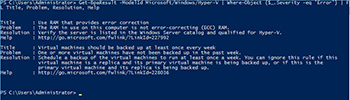 [Click on image for larger view.] Figure 4. We can filter the output to make the command more useful.
[Click on image for larger view.] Figure 4. We can filter the output to make the command more useful.
You can even dump the output to a text file by appending the Out-File cmdlet. The full command might look something like this:
Get-BpaResult –ModelId Microsoft/Windows/Hyper-V | Where-Object {$_.Severity –eq 'Error'} | FL Title, Problem, Resolution, Help | Out-File c:\results\Hyper-V.txt
In this article, I have demonstrated the basics of performing Best Practices Analyzer scans through PowerShell. However, you can build scripts that compile the results of multiple scan models and that build custom reports.
About the Author
Brien Posey is a 22-time Microsoft MVP with decades of IT experience. As a freelance writer, Posey has written thousands of articles and contributed to several dozen books on a wide variety of IT topics. Prior to going freelance, Posey was a CIO for a national chain of hospitals and health care facilities. He has also served as a network administrator for some of the country's largest insurance companies and for the Department of Defense at Fort Knox. In addition to his continued work in IT, Posey has spent the last several years actively training as a commercial scientist-astronaut candidate in preparation to fly on a mission to study polar mesospheric clouds from space. You can follow his spaceflight training on his Web site.