In-Depth
First Look: Windows Server 2012 R2 Preview
Diving into Microsoft's Windows Server 2012 R2 Preview reveals key additions to facilitate more seamless server-to-cloud migrations to public, private and hybrid clouds.
Nearly one year after Microsoft declared its plan to transform itself into a devices and services company, the key underpinnings are taking shape. The cloud, of course, is the foundation of the services driving this transformation. Microsoft's commitment to cloud computing took off in earnest three years ago when CEO Steve Ballmer famously claimed that the company was "all in," meaning the cloud would be at the center of everything the company offers.
That won't happen overnight, but last year's release of Windows Server 2012 was a key component of what Microsoft has termed its "Cloud OS" platform. While easy enough to shrug off as marketing hype, it reasonably describes the tandem 2012 releases of Microsoft System Center and Windows Server as a cloud infrastructure platform designed to enable IT to build private clouds. It can now bridge those private clouds to the public cloud, and support a mixture of the two, which is routinely described as a hybrid cloud.
With Microsoft's devices and services shift and the emphasis on transitioning Windows Server into a cloud platform, it's no surprise that the forthcoming new release offers additional capabilities designed to carry that torch. Microsoft released a preview for testers of the new Windows Server 2012 R2, which the company said should be available for general availability by year's end.
Rather than accepting Microsoft's description of Windows Server as a cloud OS at face value, it makes sense to delve a little bit deeper and take an objective look at the cloud readiness of Windows Server 2012 R2. After all, countless software vendors have simply added the word cloud to their products as a way of appealing to the masses, but have done so without adding any significant cloud-specific features.
Cloud OS Criteria
The most effective way to evaluate the cloud readiness of Windows Server 2012 R2 is to establish some basic requirements for a cloud OS. These requirements weren't provided by Microsoft and are not universal standards by any stretch of the imagination. But I personally believe a true cloud OS should:
- Function equally well in a hosted or on-premises (or even standalone) environment
- Be fluid in its ability to move resources to the cloud and bring those same resources back on-premises on an on-demand basis
- Support hybrid configurations that use on-premises and hosted resources, and do so as easily as if everything were running locally
- Offer multi-tenancy capabilities such as resource metering and resource usage control
- Provide data access without regard to a user's physical location or device type
One of the most compelling reasons for moving resources to the cloud is that clouds -- whether public or private -- are supposed to offer an unprecedented degree of flexibility and agility. As such, a good cloud OS must offer scalability that can accommodate the largest enterprises while also being able to handle the smallest deployments equally well.
Cloud Usage
Probably the best evidence supporting Windows Server 2012 R2 as a true cloud OS is that Windows Azure Infrastructure as a Service (IaaS) -- Microsoft's recently upgraded public cloud service (see "Deploy VMs in Windows Azure," June 2013, Redmondmag.com/Posey0613) -- is based on technology found in the new Windows Server OS. As of April, there were more than 200,000 Windows Azure IaaS subscribers, and in June, Microsoft claimed to be adding an additional 7,000 subscribers a week. This would suggest that Windows Server 2012 R2 is up to the task of running a large public cloud.
There are a number of features that allow Windows Server 2012 R2 to operate as a cloud OS. One is cross-premises connectivity. Microsoft introduced the cross-premises connectivity feature with Windows Server 2012 as a way of facilitating communications between two geographically separated locations. The feature uses VPN connectivity to connect an on-premises network to a private subnet on either a public or a private cloud.
The cross-premises connectivity feature was a major addition because it laid the groundwork for organizations to more easily construct hybrid networks or to establish connectivity, and begin moving services to Windows Azure.
As welcome as the cross-premises connectivity feature was, it didn't scale very well. This was a problem for apps requiring multi-tenant configurations because each tenant required a dedicated gateway. Microsoft resolved this problem in Windows Server 2012 R2 by creating a multi-tenant VPN gateway that can provide site-to-site communications to multiple external organizations. This new gateway can also be used to bridge the gap between physical and virtual networks.
It's worth noting that the virtual networking features of Windows Server 2012 were also designed to support multi-tenancy. It's possible to create multiple virtual networks with overlapping IP address spaces. Doing so helps to ensure that tenants are free to construct virtual networks to fit their needs without worrying about impacting another tenant's virtual network.
Hyper-V Live Migrations
Clouds by their very nature are highly dynamic. It might be necessary to move VMs from one host to another in response to workload changes or evolving business needs. The live migration feature, which has been a part of Hyper-V since Windows Server 2008 R2, previously worked well for on-premises deployments, but wasn't really geared toward multi-site datacenters or hybrid clouds. Thankfully, Microsoft has introduced two welcome improvements to the live migration feature.
The first of these improvements involves decreasing the time it takes to perform a live migration. Previously, live migrations were based on the use of a standard TCP/IP connection. Although this option still exists in Windows Server 2012 R2, Microsoft has provided two other options.
The first of these options is Server Message Block (SMB) 3.0-based live migrations. This feature is primarily used within a single datacenter. It uses an SMB 3.0 connection to live migrate VMs between hosts that are equipped with Remote Direct Memory Access (RDMA)-capable network adapters. The advantage is that SMB multi-channel can use multiple network adapters in the live migration process, thereby decreasing the amount of time required for the live migration to complete.
The other option for performing live migrations is the use of compression (which is enabled by default). This feature (see Figure 1,) compresses the data that needs to be transmitted prior to actually sending it to the destination host. This has the potential to make live migrations across WAN links more practical. It can be used to facilitate the movement of VMs between datacenters or between an on-premises host and a cloud-based host without causing any downtime in the process. In other words, this lets IT move a production VM to a public cloud or back on-premises without ever taking the VM offline.
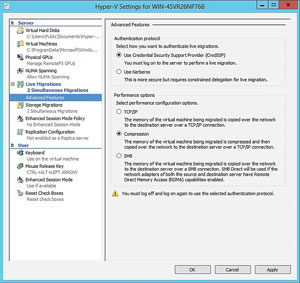 [Click on image for larger view.]
Figure 1. Live migrations can now be compressed.
[Click on image for larger view.]
Figure 1. Live migrations can now be compressed.
The second of these changes is designed to take the sting out of upgrades to the virtualization infrastructure. If an organization is running Hyper-V on Windows Server 2008 R2 and decides to upgrade to Windows Server 2012, there's no direct migration path for the VMs. Typically, the VMs would have to be exported from the old server and imported into the new server. As an alternative, some organizations have used backup and restore to migrate VMs from one version of Hyper-V to the next.
Windows Server 2012 R2 makes it possible to live migrate VMs from Windows Server 2012 to Windows Server 2012 R2. This should go a long way toward reducing the complexity of bringing Windows Server 2012 R2 into an existing Hyper-V deployment. In addition, if a company has Windows Server 2012 Hyper-V on-premises and wants to move its VMs to a public cloud that's based on Windows Server 2012 R2, it will be able to easily do so in spite of the difference in OSes.
Identity Management
For more than a decade, Active Directory has been Microsoft's mechanism of choice for authenticating users and computers, thereby establishing positive identities. Although these capabilities are still of the utmost importance in a cloud services environment, the required functionality has changed.
When Microsoft first introduced Active Directory with Windows 2000 Server, tracking user and computer identities throughout an Active Directory forest was sufficient. Today, however, a user might traverse multiple Active Directory forests on a daily basis, and his identity needs to be valid in each of these forests. Microsoft offers a number of technologies that make this possible, such as Active Directory Federation Services (AD FS) or Windows Azure Active Directory, or WAAD (see "Inside Windows Azure Active Directory,").
Things have also changed when it comes to device-level identity management. In the past computers were joined to Active Directory. Today, the Bring Your Own Device (BYOD) trend has led users to work from devices that aren't capable of being domain-joined.
Microsoft's solution to this problem is a Windows Server 2012 R2 feature that allows devices to be workplace-joined. A user will be able to download an app for his specific device and then use the app to join a workspace (which is sort of like a next-generation domain join). The enrollment process supports two-factor authentication, and the user's identity can be verified through an automated phone call. Once a device has been enrolled in Active Directory, admins can use the cloud-based Windows service to secure the device and deploy a corporate VPN profile, as well as anything else that the organization wishes to add to the device. If the user ever decides he wants to stop using his device for work, he can remove the enrollment himself. Doing so wipes any corporate information from the device, but does not cause the user's personal data, applications or settings to be removed.
Scalability and Efficiency
A cloud OS needs to be scalable, but scalability alone isn't enough. The OS needs to make efficient use of hardware resources. Otherwise, building large-scale deployments could become cost-prohibitive.
Microsoft has implemented a number of changes in Windows Server 2012 R2 that improve scalability and efficiency, but there are two changes to storage management that are especially noteworthy.
As you may recall, Microsoft introduced native file system deduplication in Windows Server 2012. Although this feature offered great potential, Microsoft put a number of restrictions on its use. The most limiting of these restrictions was the fact that Microsoft recommended not deduplicating Hyper-V hosts or volumes containing virtual desktop infrastructure (VDI) virtual hard disk (VHDs).
This limitation seemed extremely counterintuitive because volumes containing virtual servers or virtual desktops typically contain a tremendous amount of redundancy. Fortunately, Microsoft has changed its policy in Windows Server 2012 R2. In fact, Microsoft has even indicated that deduplicating volumes containing VDI VHDs can actually improve performance.
Another notable change is the inclusion of a storage-tiering feature (see Figure 2,). It's now possible to construct a volume in a way in which hot blocks (the blocks that are read most often) reside on solid-state drive (SSD) storage, while cooler blocks remain on traditional storage.
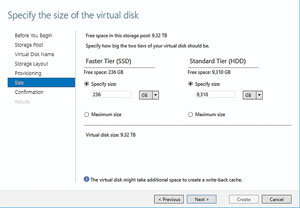 [Click on image for larger view.]
Figure 2. Storage tiering can help with storage performance.
[Click on image for larger view.]
Figure 2. Storage tiering can help with storage performance.
Obviously, caching hot blocks on SSD has the potential to greatly improve a volume's performance, but if Microsoft allows storage tiering and deduplication to be used on the same volume, it should offer an extreme performance benefit, especially in VDI environments.
Multi-Tenancy
One characteristic of clouds (both public and private) is that they must be able to handle a number of different customers. Public clouds offer services to paid subscribers. Private clouds often provide resources to authorized users within the organization, but use chargebacks to bill individual business units for the resources they consume. In any case, a cloud must support multi-tenancy.
Windows Server 2012 R2 obviously supports multi-tenancy. Otherwise, Microsoft would not be able to use it to run Windows Azure. Even so, most of the better-known multi-tenancy features are found in System Center as opposed to the core OS.
Of course, that's not to say no multi-tenancy features are built into Windows Server 2012 R2. One of the most useful multi-tenancy features exists in Windows, but can't be enabled through the GUI. The feature is Hyper-V resource pools.
Hyper-V resource pools are different from VMware resource pools. Rather than providing a pool of hardware resources to a collection of VMs, Hyper-V resource pools keep track of the resources that a collection of VMs is using. Doing so is useful for both chargebacks and for capacity planning in multi-tenancy environments.
These resource-monitoring capabilities actually existed in Windows Server 2012 Hyper-V, but many administrators didn't realize it because the capabilities were hidden from the GUI. However, considering Microsoft is creating Windows Server 2012 R2 with the specific goal of having it act as a cloud OS, resource-usage tracking will undoubtedly become more important.
Operating systems have new key criteria in order to fit the bill as true cloud OSes. The features and capabilities that exist in the new Windows Server 2012 R2 Preview release appear to do a good job of directly addressing these criteria.