
The most perilous moments in a spaceflight can happen after the landing.

Your personal data is just as vulnerable to disk failures and ransomware as corporate data. But right now, there are threats that are more difficult to protect against: wildfires and hurricanes.

Despite the strangeness of the keynote, Microsoft pulled off some its most geek-worthy product demos at Ignite this week.

Something about Satya Nadella's opening keynote makes Brien wonder if Microsoft thinks we'd all be better off doing everything -- including conferences like Ignite -- remotely, even after the pandemic is over.

Microsoft now lets Microsoft 365 connect to various data sources -- whether in the cloud or on-premises -- so that those data sources can be indexed for searching.

Because sometimes (a lot of the time), Protected View isn't enough to guard against potentially malicious Office documents.

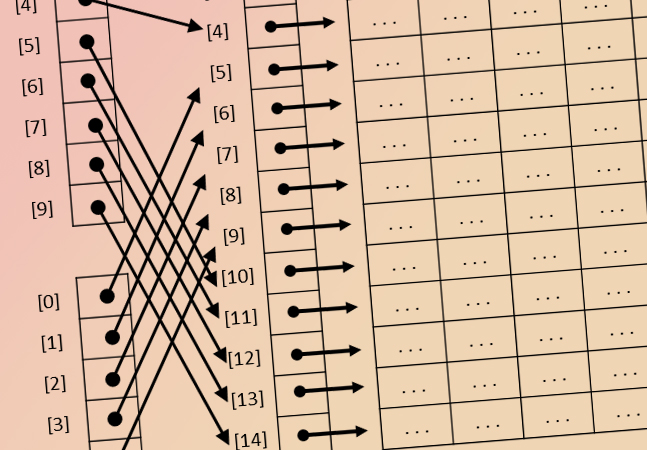
In the second part of this series, Joey describes the methods that Microsoft uses to manage code rollouts, and how it detects hardware and software problems on Azure SQL.
- By Joey D'Antoni
- 09/10/2020

Microsoft promises 99.995 percent uptime for the Azure SQL platform, which is incredible. In the first of a two-part series, Joey takes an close look at the infrastructure that supports high availability in Azure database services.
- By Joey D'Antoni
- 09/08/2020

Ignite is Microsoft's most important event of the year. What direction will Microsoft take for Ignite's first-ever virtual outing, during the IT industry's most challenging year on record?
Why did Microsoft go with Android and not Windows 10? Why aren't other Surface devices supported? Microsoft's upcoming Surface Duo might end up being brilliant, but for now it has us scratching our heads.

Since Microsoft acquired it in 2012, Yammer has been the odd application out. Microsoft's latest updates bring the chat application closer to the rest of the Microsoft 365 family.
Space is a very unforgiving environment, and it's critical to use the correct procedures when emergencies occur. That's a big part of why aerobatic flight is so important.
One of the best new features in PowerShell 7 is the ability to perform parallel execution of script blocks, which can drastically reduce the amount of time it takes to process ForEach-Object loops.
To avoid errors, it's important to write PowerShell scripts that prevent code from running on an unintended platform. Luckily, this is easier to do than it sounds.

IT pros are working long hours right now to keep their organizations afloat during the COVID-19 pandemic. But that shouldn't be the expectation once the crisis passes.

With much of the corporate world now interacting via online chat, Microsoft is throwing a bunch of new features at its Teams platform, hoping that at least a few of them will stick. But chat bubbles?

The next wave of technical innovation will be driven by businesses looking to provide more touchless experiences to their coronavirus-wary customers.

Commercial space training isn't all about research. Sometimes -- especially when the gravity is out -- the crew gets to cut loose.

Microsoft's Hyper-V snapshots feature is a convenience, not a backup replacement. But with different cloud vendors using the term "snapshots" in different ways, that's easy to forget.

With cloud suites like Microsoft 365 scattering user data across multiple apps and services, application-aware backups and restorations are due for a surge in renewed interest.