In-Depth
It's Time To Go Passwordless -- Here's How
Microsoft has provided the tools for you to ditch the outdated and unsecure log in tech. It's up to you to actually take advantage of it.
- By Joey D'Antoni
- 10/28/2022
One of the key topics at Microsoft Ignite 2022 was the security enhancements within Windows 11, and how some of these features tie back into Azure Active Directory. As mentioned in the latest Microsoft Authenticator news story, some parts of these features have reached "general availability." During Ignite, I had the opportunity to speak with the PM team to be understand some of these enhancements.
Everyone needs passwords to provide some baseline level of security. The problem is most users practice bad password hygiene because passwords are terrible. I used to have terrible password practices, including using a standard password with minor changes depending on the account in use. Finally, after several data breaches, my password was compromised and I decided to follow best practices. After that, I started using a password manager (1Password) and enabling multi-factor authentication (MFA) on most of my accounts, especially important ones like banks.
At my job at DCAC, all of our team uses password managers and multi-factor authentication. However, we are a very small team of very experienced technology professionals. A contrast is that I've been trying to get my dad (unsuccessfully) to use a password manager for several years now. As you all know, helping your end users have better security hygiene is a big challenge.
Adding security always adds a burden to users. I saw an example of this when working with a colleague this morning. He had to use Microsoft Authenticator to authenticate to a clients VPN, and then Duo to MFA into a remote desktop session. While making administrative logins more burdensome can be a valid security tradeoff, if you made your non-admin users use three authentication factors, it would likely raise the ire of most of your those users. This leads to the question: how do you ensure the identity security of your business users while trying to avoid the hardship of complex authentication procedures? You can see the chart below highlighting security versus burden.
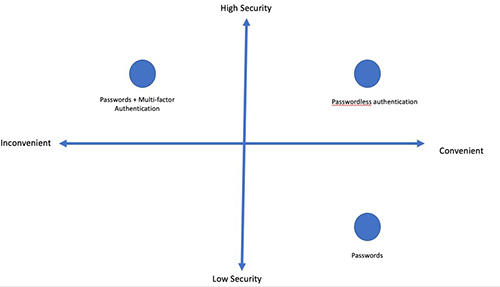 [Click on image for larger view.]
Figure 1.
[Click on image for larger view.]
Figure 1.
For many years Microsoft has been pushing to reduce the dependency on passwords for the login process. Internally, Microsoft first used smart cards as part of its secure authentication process. Beyond smart cards, which had a high administrative cost, Windows Hello and
device PINs reduce the dependence on passwords.
As IT admins, this can be somewhat confusing -- some may ask how PIN more secure than a complex password. While it seems like a PIN is just a less complex password, the full story is more complicated than that. A local password is authenticated against the machine's password store, while online passwords (like Active Directory) are validated against a server password store. A PIN is also tied to a device. If I have your AD password, I can log in to any machine in the domain, but if I have your PIN, I can only log in to your machine and I have to be in physical possession of your machines.
Beyond just remaining local, modern computers have what is known as a Trusted Platform Module (TPM) chip, which has tamper protections and reduces the risk of malicious software. The TPM v2 requirement was somewhat controversial for Windows 11 devices, as it meant older PCs could not support Windows 11. However TPM 2.0 supports additional both stronger algorithms and better performance.
Whether the user is using a PIN, a biometric ID (like facial recognition or fingerprint) or even a FIDO2 device like a YubiKey, the basics of the process are the same. The TPM is at the heart of the modern authentication strategies.
Let me give you an example: Windows Hello generates a cryptographic key pair which creates a trust relationship between the identity provider and the user, and then sends the public portion of a private/public key pair, to the identity provider (which can be a Microsoft account, AD or Azure AD) and then associated to the user account. Simply, the PIN or biometric authentication derives a key which is mixed into the TPM to release a key, which is then used to authenticate.
Whether you use Intune and Mobile Device Management, or Active Directory with group policy, you can enable Windows Hello across all your organizations devices. You should note that Hello for Business is designed to be managed by either Intune MDM or Active Directory GPO, but not both. When you combine Windows Hello for Business with Azure Active Directory single sign-on, your users can access their applications with a frictionless experience tied to Windows Hello for Business.
Maintain Admin SecurityWhile securing the logins of your users is important, securing the accounts of administrators is the biggest element in most security strategies. Azure AD already supports Privileged Identity Management and Conditional Access features, which are the hub of good security posture. One of the recent additions to Azure AD, which was announced at Microsoft Ignite, is using strength of Authentication in conjunction with Conditional Access.
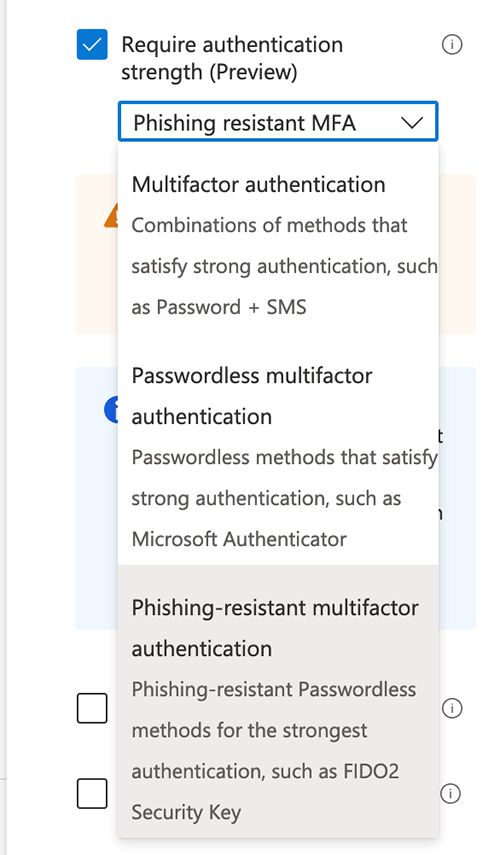 [Click on image for larger view.] Figure 2.
[Click on image for larger view.] Figure 2.
To explain just one of the ways you can use this, in our Azure AD tenant we created a conditional access policy that requires a group of users (in this case our consultants) to use a phishing-resistant MFA authentication method if Azure AD determines their login to be of a medium or high risk level (Azure AD classifies all logins with a risk at level at initial login based on a number of factors).
Our default approach is to use Microsoft Authenticator with number matching, which protects you against a "MFA fatigue" attack (where your credentials have been compromised and an attacker is spraying your mobile device with 100s of MFA authentication requests in the hopes that the targeted user will accidentally accept one). With number matching, the user needs to type in a number that is displayed on the device where they are authenticating, which greatly reduces the risk of these attacks.
FIDO2 physical keys, like YubiKey, take this process a step further by storing a certificate on the token. This means that if a user clicks on a phishing email from an attacker, with a link to an attacking site (like myaccount.micros0ft.com), the YubiKey (which would contain information for myaccount.microsoft.com) would spot the mismatch and simply not allow credentials to be shared.
I Can Do This for Everything, Right?
While Microsoft has built a robust and secure authentication platform with Windows Hello for Business and Azure Active Directory, every application in the world does not support these authentication methods. There are even Azure applications (I'm calling out Azure SQL Database here) which don't support passwordless AAD authentication. However, you can protect your critical Azure and Microsoft 365 assets with these
Beyond Microsoft, most of the applications that support single sign-on (SSO) with AAD can be compatible, but that doesn't mean all (especially third-party applications) support these latest authentication methods. I met with a vendor this week that had critical infrastructure that still allowed basic authentication to their application.
So my closing message is to both program managers in various software companies (including Microsoft) to support these stronger authentication methods and to allow administrators to disallow authentication with weaker methods.
About the Author
Joseph D'Antoni is an Architect and SQL Server MVP with over two decades of experience working in both Fortune 500 and smaller firms. He holds a BS in Computer Information Systems from Louisiana Tech University and an MBA from North Carolina State University. He is a Microsoft Data Platform MVP and VMware vExpert. He is a frequent speaker at PASS Summit, Ignite, Code Camps, and SQL Saturday events around the world.