News
Microsoft Describes Windows Update for Business Limitations and Dual Scan Caveats
Microsoft this week described Windows Update for Business (WUB) and how it plays with System Center Configuration Manager (SCCM) when managing Windows 10 clients.
Based on a recorded talk by Steven Rachui, a Microsoft principal premier field engineer, WUB doesn't exactly play very well with SCCM right now. The combination can have unexpected effects. For instance, users might not see Windows 10 update compliance reporting in SCCM. In addition, using WUB with SCCM will trigger the infamous "dual scan" behavior that a year ago tripped up IT pros. They turned on settings that looked like they'd defer Windows 10 updates from arriving, but instead those settings triggered delivery.
Microsoft officials later explained that dual scan was intended to be a feature rather than a software flaw. Dual scan was added to expand Windows 10 client management options for organizations, they contended.
What Is Windows Update for Business?
WUB has been in Windows 10 since version 1511, but Microsoft hasn't always been able to articulate exactly what it is. Rachui said that WUB typically gets described as "a free cloud service," but it's not really that. It has a cloud aspect, but it's really just a series of settings specific to Windows 10 that are available for IT pros to use.
He showed the WUB capabilities that have been added to various Windows 10 versions in this slide:
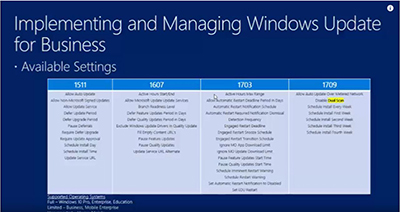 [Click on image for larger view.] Windows Update for Business additions to Windows 10 versions. Source: Microsoft Web presentation by Steven Rachui.
[Click on image for larger view.] Windows Update for Business additions to Windows 10 versions. Source: Microsoft Web presentation by Steven Rachui.
WUB can be used to manage feature and quality updates for Windows 10 clients. It doesn't require extra infrastructure to use its capabilities, and there's no software to install. The WUB configuration gets set by IT pros and it takes care of itself. There are no approval cycles each month for Windows 10 clients when using WUB, and no deployments to manage each month.
"You can do some organization with Windows Update for Business, but it's not an ongoing process for admins," Rachui said. He contended that with Windows 10, organizations shouldn't need to choose which updates to deploy month to month. Instead, they can set configurations in WUB and then just let the updates run.
WUB is "very configurable," according to Rachui. Settings can be configured manually using the Windows 10 client user interface, Group Policy, the registry, Microsoft Intune or a mobile device management solution, and SCCM. During the talk, Rachui demonstrated some of those details.
WUB can be used with Windows 10 "servicing rings," which is a kind of triage approach for delivering updates to client devices in organizations. It supports the "maintenance windows" that organizations may have. It works with Microsoft's peer-to-peer "Deployment Optimization" caching capability to manage bandwidth during PC updates. It also works with existing management tools, including as a standalone tool. It'll work in conjunction with Windows Server Update Services (WSUS), SCCM, the Microsoft Enterprise Mobility + Security (EMS) suite and even third-party tools, Rachui indicated.
WUB has some requirements. It needs to have Internet connectivity and at least Basic telemetry needs to be turned on. It only works with Windows 10 clients, including the Education, Pro and Enterprise editions. It doesn't support the Windows 10 Mobile edition.
Current Limitations
In order for SCCM to manage a Windows 10 system and apply WUB settings to it, that system needs to be running Windows 10 version 1703. Rachui clarified that IT pros can apply WUB settings to previous Windows 10 versions, but they just can't use SCCM for client management in those cases. Instead, they should use Group Policy Objects (GPO), he suggested.
Monitoring when using WUB can be somewhat nuanced. When using WUB with Microsoft Intune, there's a way to monitor the use of software update rings. When using WUB with SCCM, though, there are some monitoring caveats.
"Config Manager works great for reporting results for systems it patches, but for Windows Update for Business, there is no ability for Config Manager to apply the patches to systems, so it's not going to get the status data back too easily," Rachui said.
In other words, there's no reporting of Windows 10 update status through SCCM when using WUB.
Organizations using WUB with SCCM should turn off the "Software Updates on Clients" setting in SCCM because "you're letting Windows Update for Business take care of things," Rachui later explained.
Another limitation when using SCCM with WUB concerns policy settings for "Active Hours," which specifies when an end user's PC can get updated. Right now, it's not possible to configure Active Hours through SCCM.
Microsoft's conditional access schemes, which provide a check to determine if devices meet with IT-defined policies, have limitations when using SCCM with WUB. "We don't know the compliance status in SCCM," Rachui explained.
There are a few other limitations when combining SCCM with WUB, according to Rachui. He said that "definition updates won't work as expected." SCCM won't be able to deploy updates "like Office or IE or Visual Studio" because the software update agent is turned off. It won't be possible to deploy third-party updates published to a local WSUS, he added.
"Those are a lot of caveats," Rachui admitted, but he claimed that WUB may work for some scenarios in organizations. WUB should be considered as just another tool that's available in an organization's toolbox.
Dual Scan
Rachui shed some light on the dual scan topic. He clarified that the combination of SCCM use with WUB definitely will trigger dual scan behavior.
"If you are using Config Manager to configure your Windows Update for Business deferral policies, by default that means the Window 10 system where those configurations are applied through Config Manager will be enabled for dual scan," Rachui said.
Instead of going in that direction, organizations today can try using GPO to deploy WUB polices and avoid the dual scan behavior. That's possible when using SCCM version 1706, he clarified.
If an organization finds that they can't patch Windows 10 clients in bulk, then they likely enabled dual scan, Rachui noted.
Dual scan is an updated configuration in the Windows 10 client and has been available since the Windows 10 version 1607 release, Rachui explained. The updated configuration changed how the Windows client worked. Historically, the Windows client talked to WSUS. However, if dual scan is enabled, the client will no longer look to WSUS. Instead, it'll look to the Microsoft cloud service to get updates.
Microsoft enabled the ability to use dual scan because of a trend toward "modern management."
"As more organizations progress to modern management, being able to shift to the cloud for updates is a desirable thing," Rachui said, although he added that "the impact to SCCM clients was pretty notable."
Windows 10 version 1607 doesn't have a specific setting to enable dual scan. However, dual scan can get accidentally or intentionally enabled when IT pros pair two settings.
"The way it [dual scan] gets enabled is there's one main setting specifying the intranet Microsoft update service location and if you pair that with either the 'Select when feature updates are received' or 'Select when quality updates are received,' [then] you are turning on dual scan," Rachui explained.
He described one scenario that inadvertently triggered dual scan.
"Admins rightly wanted to be able to say, 'No, I want to control when feature updates are received,' so they started making those configurations in GPO, but they also had the first setting enabled, and magically we now have dual scan enabled and SCCM updates are broken."
As of Windows 10 1709, there is now a setting in GPO called, "Don't allow configuring deferral to cause dual scan to turn on." It blocks the dual scan behavior, Rachui explained.
If an organization wants to use SCCM to deploy update deferral policies for Windows 10 clients, then they'll want to be on SCCM version 1706. The SCCM version 1702 client will accept the deferral policies, but it'll periodically blank them out, Rachui noted.
About the Author
Kurt Mackie is senior news producer for 1105 Media's Converge360 group.