In-Depth
How To Connect Azure AD to Office 365
Learn how to use Azure Active Directory with Microsoft Office 365 and understand the benefits of integrating them.
Office 365 customers can use Azure Active Directory (Azure AD) for free, although some of its capabilities entail paying for subscription costs. Office 365 has its own local directory. There's no requirement to use Azure AD, which is an identity and access management service housed in Microsoft's datacenters. For some organizations, doing without Azure AD may be their approach.
Even so, there are numerous benefits to using Azure AD and it's relatively easy to configure. For instance, you don't have to set up Active Directory Federation Services (AD FS) or make DNS-level changes.
Configuration Steps
To configure Office 365 to use Azure AD, log into the Office 365 console, and then go to the Azure AD Admin Center, located with the other Office 365 Admin Centers. A new browser window will automatically open, directed at the Microsoft Azure subscription page. Create an Azure AD subscription by entering some basic information such as your name, e-mail address and phone number. When I worked through this process, I wasn’t required to provide a credit-card number.
Upon entering all the required information, a message will note that the setup will take a few minutes. In my case it took less than a minute.
Once Azure AD is provisioned, you should have access to your directory through the Azure AD Admin Center. The easiest way to tell whether the process worked is to click on the AD container. You should now see a directory listed whose name matches that of your Office 365 account. In my case, for example, the directory is called Posey Enterprises (see Figure 1).
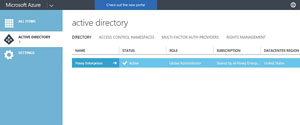 [Click on image for larger view.]
Figure 1. An organization’s directory listed within Azure AD.
[Click on image for larger view.]
Figure 1. An organization’s directory listed within Azure AD.
Now, click on the arrow icon located just to the right of the directory name. This will take you into the directory. If you click on the Users tab, you should see a list of your Office 365 users (see Figure 2).
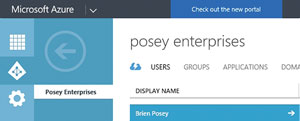 [Click on image for larger view.]
Figure 2. Your Office 365 users should be listed within Azure AD.
[Click on image for larger view.]
Figure 2. Your Office 365 users should be listed within Azure AD.
The Case for Azure AD
Microsoft makes it very easy to link Office 365 to Azure AD, but you may be wondering what the benefit is of doing so. After all, the directory service built into Office 365 seems to work just fine.
Azure AD provides a number of capabilities, such as the ability to offer self-service password reset capabilities to your users, and the ability to generate a number of different security and usage reports. Before I further describe Azure AD features and capabilities, however, it’s important to understand that there’s more than one Azure AD subscription type, and Azure AD features and capabilities vary significantly by subscription type.
Initially, Microsoft offered a basic Azure AD subscription, and a more capable subscription, Azure AD Premium. Although the Azure AD Basic subscription still exists, there are now two different Azure AD Premium subscriptions: P1 and P2. The difference between the premium subscriptions is that the P2 subscription includes identity protection and privileged identity management capabilities, whereas the P1 subscription does not.
In addition to the Premium and Basic subscription plans for Azure AD, Microsoft also offers a free Azure AD, and an unnamed plan that applies only to Office 365. The Azure AD subscription included with Office 365 is more feature-rich than the Azure AD Free plan, but does not have all of the capabilities of Azure AD Basic.
Noteworthy Features
The version of Azure AD included with Office 365 is better than the free version for a number of reasons. First, the Office 365 version of Azure AD doesn’t have an object limit, at least not with Office 365 user accounts. In contrast, the free plan has a 500,000 object limit. Although half a million objects admittedly sound like a lot, a midsize organization could potentially reach this limit rather quickly.
Another reason the Azure AD included with Office 365 is better than the free version relates to the service-level agreement (SLA) that Microsoft provides. The Office 365 version of Azure AD includes an SLA of three-nines (99.9 percent availability). Conversely, the free version doesn’t include an SLA. The Azure AD Free version is likely every bit as reliable as the Office 365 version of Azure AD. Even so, it wouldn’t make sense for Microsoft to provide an SLA with Azure AD Free, because SLAs are usually financially backed.
The Office 365 version of Azure AD also includes a portal that users can use for self-service password resets. Furthermore, the log-on pages and other portions of the Azure AD environment that may be exposed to the end user can be custom branded by the organization that’s using it. Self-service password resets and custom branding capabilities aren’t included with the free version of Azure AD.
As previously noted, Azure AD Basic includes some capabilities that aren’t included with the Office 365 version of Azure AD. Azure AD Basic includes group-based access management and provisioning, as well as an application proxy feature, neither of which are included with the Office 365 version of Azure AD.
Premium Features Included
There are a number of features included with Azure AD Premium. Among them are multifactor authentication, cloud app discovery, and conditional access based on things like group membership, location, and device state.
This raises the question of whether it’s possible to upgrade Office 365 to use a better version of Azure AD. The Azure AD console provides an option for upgrading to Azure AD Premium, but there’s no obvious way of upgrading to Azure AD Basic. However, if you already have an Azure subscription separate from Office 365, it’ll include Azure AD Basic (unless you’ve opted to purchase Azure AD Premium), and you should theoretically be able to configure Office 365 to use the existing Azure subscription, rather than setting up a dedicated copy of Azure AD. However, I haven’t had the opportunity to test this and the documentation is somewhat unclear with regard to the ability for Office 365 to use Azure AD Basic.
Just as Microsoft routinely adds new features and capabilities to Office 365, it’s worth noting the company also continuously updates Azure. I don’t really anticipate Microsoft introducing any new features for the Office 365, Basic or Free versions of Azure AD any time soon, but Microsoft does occasionally offer new features to its Azure AD Premium subscribers. In fact, Microsoft has recently announced a public preview of its Network Policy Server (NPS) extension to Azure Multi-Factor Authentication (MFA).
Azure MFA is an Azure AD Premium-only feature. The new extension to this feature will allow Azure AD Premium subscribers protect their Windows-based VPN through Azure AD (Microsoft posted a description about the preview here).
Working with Azure AD
Clicking on the listing for your organization within the Azure AD Admin Center takes you to a screen where you can manage various aspects of the AD environment. The interface includes a series of tabs that run along the top of the screen. The default tab is the Users tab (in Figure 2). This tab contains an option
for adding users, but it is generally advisable to create new users from within the Office 365 Admin Center rather than from within the Azure AD Admin Center, because creating user accounts directly within Azure AD has been known to cause problems regarding the Office 365 provisioning and licensing process.
Selecting the Users tab directs you to a screen that allows you to access and modify information related to the user account. You can access the user’s basic profile information, job information, contact information, a list of the user’s devices and a log of the user’s activity. Azure AD doesn’t expose quite as many user attributes as the AD Users and Computers console does, but it does provide a significant number of user-specific fields (see Figure 3).
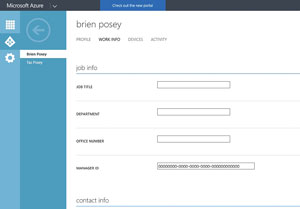 [Click on image for larger view.]
Figure 3. The Azure AD interface allows you to populate a number of user attributes.
[Click on image for larger view.]
Figure 3. The Azure AD interface allows you to populate a number of user attributes.
Reporting Options
Another area of the Azure AD interface that is sure to be of interest to Office 365 administrators is the Reports tab. Although the Azure AD implementation that comes with Office 365 doesn’t offer the advanced reporting capabilities that are included with Azure AD Premium, it does feature an impressive number of reports. These reports deal with things such as Licensing, Anomalous Activity, User Activity and External Access (see Figure 4). Incidentally, the reports listed in the Premium Reports section are only available to Azure AD Premium subscribers.
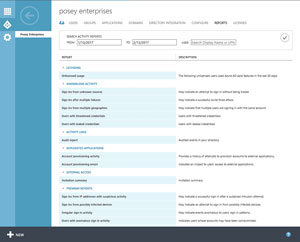 [Click on image for larger view.]
Figure 4. There are a significant number of reports included with Azure AD.
[Click on image for larger view.]
Figure 4. There are a significant number of reports included with Azure AD.
Create and Manage Groups
While there are too many available tabs to describe, one worth emphasizing is Groups, which lets you create and manage Active Directory groups. This tab allows for the creation of two different group types: Security groups and Office 365 Preview groups. Most should be familiar with Security groups, but Office 365 Preview groups are worth noting.
Office 365 Preview groups are just a new Office 365 group feature that is currently in preview. These groups are hosted in the cloud, but have on-premises write-back capabilities. This means an on-premises Exchange mailbox server can use an Office 365 group as a distribution group.
Although there’s no rule that says that you have to connect Office 365 to Azure AD, Azure AD will likely prove to be beneficial. Azure AD allows Office 365 user accounts to be managed at a more granular level than what’s possible through the Office 365 console. In addition, Azure AD provides some nice reporting capabilities.
About the Author
Brien Posey is a 22-time Microsoft MVP with decades of IT experience. As a freelance writer, Posey has written thousands of articles and contributed to several dozen books on a wide variety of IT topics. Prior to going freelance, Posey was a CIO for a national chain of hospitals and health care facilities. He has also served as a network administrator for some of the country's largest insurance companies and for the Department of Defense at Fort Knox. In addition to his continued work in IT, Posey has spent the last several years actively training as a commercial scientist-astronaut candidate in preparation to fly on a mission to study polar mesospheric clouds from space. You can follow his spaceflight training on his Web site.