News
Microsoft Experts Outline Windows 10 Tips and Tools
Experts at Microsoft clarified a few more Windows 10 deployment and management matters this week.
The details were discussed in a Thursday online presentation by Michael Niehaus, director of product marketing for Windows Commercial, and Nathan Mercer, senior marketing manager for Windows Commercial. The presentation will be available on demand at some point, they promised.
The talk centered on Window 10 features for IT pros. It largely recapped the new tools that IT pros can use for Windows 10. There are tools for imaging and deployment, as well as assessing computing-environment readiness for Windows 10.
In terms of application compatibility, Mercer said that Microsoft's customers have been reporting 99.9 percent application compatibility with their Windows 10 upgrades. A Ready for Windows site can be used to check application compatibility. Users just type the program's name to see what's known.
Mercer added a caveat for Windows 7 holdouts. He said that there are just 992 days remaining until Windows 7 will hit its end of life.
Reliability Updates
Earlier this week, Microsoft had announced that Windows 10 is now getting cumulative nonsecurity updates each month, possibly more than one per month. While Niehaus had originally suggested in comments that this approach would add two weeks additional time for IT pros to test nonsecurity updates, the timing wasn't explained. In response to a question during the presentation about when these new cumulative nonsecurity updates (or "reliability updates") will arrive, the Microsoft team offered the following response:
Security Updates are on the 2nd Tuesday of the month. Reliability Updates are the 4th Tuesday. Patch Tuesday patches will include the month before's reliability updates since they are cumulative.
Based on that response, it seems that these new reliability updates will arrive on "D" week, although it may not be a firm schedule. The two weeks testing time is the interval that precedes the next month's patch Tuesday release. Here's how that scheme looks in table form:
| Update Name |
Scope |
Publish Method |
Windows Update? |
| Security-only quality update |
Monthly (only security patches) |
On "B week" to WSUS and the Windows Update Catalog; accessible via SCCM |
No |
| Security monthy quality update (a.k.a the "monthly rollup") |
Cumulative (security plus non-security patches) |
On "B week" to WSUS and the Windows Update Catalog |
Yes |
| Preview of monthly quality update (a.k.a the "preview rollup") |
Cumulative (security plus non-security patches) |
On "C week" to WSUS and the Windows Update Catalog |
Yes |
| Non-security only quality updates (a.k.a. "update"), arriving once or more per month |
Cumulative (non-security only updates) |
On "D" week to WSUS and the Windows Update Catalog; accessible via SCCM |
Yes |
Table 1. Nomenclature and timing for Microsoft's monthly security updates for supported Windows clients and servers, starting on Oct. 11, 2016. The cumulative updates will start to include all past fixes by early 2017. "B week" represents "patch Tuesday," or releases that occur on the second Tuesday of each month. "C week" represents releases that occur on the third Tuesday of each month. "D week" represents releases that occur on the fourth Tuesday of each month. WSUS, Windows Server Update Services; SCCM, System Center Configuration Manager. Source: Microsoft Windows blog post and Enterprise blog post, plus April 2017 talk by Niehaus and Mercer.
|
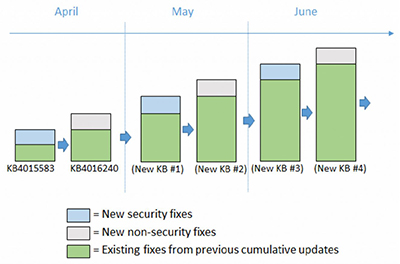
The original announcement of this scheme was substantially revised by Microsoft. The revised blog post now has a chart illustrating the cumulative nonsecurity update approach each month:
 [Click on image for larger view.]
Figure 1. Monthly cumulative nonsecurity updates for Windows 10. Source: Microsoft blog post.
[Click on image for larger view.]
Figure 1. Monthly cumulative nonsecurity updates for Windows 10. Source: Microsoft blog post.
It's not really clear exactly when multiple reliability updates might arrive. It's not that important, though. The revised announcement now explains that it's possible to skip them "since the same fixes will be included in the next 'Update Tuesday' cumulative update (along with all the new security fixes)."
The Microsoft team was also asked during the presentation whether the "current branch" and "current branch for business" terms used for Windows 10 would get dropped. Surprisingly, the team indicated it's "working on that," adding that "we do want to update the terminology used for Windows as a service to simplify it and to align with Office, more to come on that."
Microsoft recently announced that it has swapped out its Office 365 ProPlus servicing names and decided on a regular March and September release cycle for its major feature updates to Office 365 ProPlus and Windows 10.
Management
Niehaus talked a bit about Windows Update for Business, which is a set of management capabilities associated with Group Policy. Windows Update for Business can be used to configure policies to establish deployment rings for testing Windows 10 with groups of end users. Based on feedback, Microsoft has added deferral options to it.
"In the case of Windows 10 1703, the biggest change is that we expanded the time that you can defer feature updates," Niehaus said regarding Windows Update for Business. "So now, instead of up to 180 days, we can stretch it out to 365 days."
He added that organizations shouldn't defer for the full 365 days, though, because it would permit just two months' use of the operating system before the next feature update arrives.
Microsoft also supports Express Updates for Windows 10, which addresses the size of updates, which are cumulative. Express Updates allows the update process to be smart about what gets delivered to each machine, Niehaus said. Organizations using management systems such as Windows Update, Windows Update for Business and Windows Server Update Services are already using Express Updates. It downloads roughly 100MB of content per machine per month when using those management systems.
"With machines that today would be using Configuration Manager to patch a Windows 10 machine without Express Updates, it might be downloading more like a gigabyte per machine per month," Niehaus added.
Express Updates works with System Center Configuration Manager version 1702. However, it needs to be turned on for the server side to download the full update and the Express Updates package that goes along with it, and it also needs to be enabled on the client side as well, Niehaus said.
Initially, Express Updates for System Center Configuration Manager may look a bit hefty, Niehaus explained.
"The full update might be a gigabyte; the Express Update might be 5 gigabytes," Niehaus said regarding the use of Express Updates with System Center Configuration Manager. However, with it turned on, the client becomes smarter about what it gets downloaded. It just delivers the changed bits. It delivers around 100MB per month per PC, he explained.
Deployment and Other Tools
There was a quick recap on deployment, security and planning tools during the presentation.
Mercer said that "there is no new Remote Server Administration Tools [RSAT] downloads needed for Windows 10 1703." He added that RSAT "will actually install itself as part of the feature update process, so you will need to reinstall this on your admin PC if you do an upgrade." The Windows 10 version 1607 RSAT should be used with Windows 10 version 1703, he explained.
There's a new version of the Windows Assessment and Deployment Kit (ADK) that's specifically for Windows 10 version 1703, Mercer noted.
Windows Configuration Designer is a configuration tool that lets IT pros perform Azure Active Directory bulk enrollments and it also can remove preinstalled software. When using the tool for bulk Azure Active Directory enrollments, the tool uses bulk-enrollment tokens that are only good for a month, so "you have to update the provisioning package each month to include the latest tokens," Niehaus explained. When using this tool to remove preinstalled software, the process will reset the PC and will add about 20 minutes to 30 minutes to the upgrade process, he added. Windows Configuration Designer is available as an application through the Windows Store or via the Windows ADK, Mercer said.
The MBR2GPT tool converts Windows 7 BIOS PC disks to the Windows 10 UEFI GPT layout, enabling secure boot. Niehaus said that it takes a minute or so to convert each machine, and it can be triggered as part of a deployment process after upgrading a Windows 7 machine to Windows 10. It preserves the data on the machine.
Windows Defender Antivirus is the new name for the Windows Defender antimalware program that comes with Windows 10. It has a Block at First Sight feature that uses Microsoft's cloud to speed up malware blocking.
Microsoft sells a separate post-breach analysis service called "Windows Defender Advanced Threat Protection, which is built into the kernel of Windows 10. It taps an agent running on Windows 10 PCs that can talk back to Azure machine learning to gain insights. The service has diagnostic capabilities, including the ability to drill down into user details.
Windows Hello for Business is Microsoft's biometric access feature in Windows 10. It used to require using Azure Active Directory connections. Now, it can be run completely on premises. The documentation on TechNet will be coming over the next month or so, Microsoft promised.
There's a new tool to check Group Policy settings for a user of mobile devices. It's called the Mobile Device Management Migration Analysis Tool (MMAT).
Organizations planning Windows 10 upgrades can use a couple of free tools, Mercer said. The tools use an agent that gets deployed on a cross-section of machines, he added. There's an Upgrade Readiness tool, which is currently available, and an Update Compliance tool, which is in beta. The Update Compliance tool will show how many machines have been patched or have not been patched. It will let IT pros see why patches didn't install, Mercer said.
More Resources
Microsoft this week has been pointing to various Windows 10 resources for IT pros. It is now publishing its Windows 10 documentation at docs.microsoft.com, rather than in the TechNet library, Mercer announced.
The Windows IT Center is still available with labs and demos. There's also a new Microsoft Virtual Academy course on Windows 10 security.
Niehaus offered guidance on how to find Windows 10 Language Packs, which apparently can be confusing.
Lastly, Microsoft is now promising to clear up confusion surrounding a so-called "dual-scan" behavior that can occur for System Center Configuration Manager users when they attempt to defer Windows 10 updates. Steve Henry, a program manager for Windows Server Update Services, indicated in a blog post this week that information would be arriving "next week," and that Microsoft was preparing "a workaround."