
Windows Server has a built-in iSCSI initiator that it can use to connect to an iSCSI target. Before it can do so, however, you'll need to enable and configure the initiator. Here's how.

If the hardware behind your domain controllers has become outdated, here's a step-by-step guide to performing a hardware refresh.

So you want to know whether a Hyper-V virtual machine built on a legacy host will be supported by a newer server? There's a PowerShell command for that.
Datacenter solutions vendor Kaloom this week unveiled a new offering the company says will enable the development of "self-driving" datacenter networks.
- By John K. Waters
- 06/19/2019

It's time again for Brien to perform a major storage upgrade on his Hyper-V hosts. But this time, he's taking a new approach.

While the overall look and feel of Office 365 is pretty standard across organizations, there are several ways to personalize it and make it fit better with your company's specific needs.

For decades, group policies have been the go-to method for securing devices on a Windows network. In this age of BYOD, however, that may not be enough.
Brien walks you through the basics of building a PowerShell script that examines remote servers one at a time.

There are plenty of reasons to make Hyper-V VMs portable. The key is to make sure they work consistently, regardless of where each VM is running. Here's how to do it.

Hyper-V in Windows 10 has a built-in tool called Quick Create that lets you automate the process of setting up new virtual machines. Here's how to use it.

With hackers infiltrating one in three Office 365 customers, an IT pro's best bet is to be suspicious of almost everything.

How Microsoft is using its "Your Phone" and "Launcher" apps to sneakily turn Google's smartphone platform into (almost) the mirror image of its own.

Hyper-V replication failures happen rarely, but their impact can be catastrophic when they do. Know the scenarios that are likely to trigger a replication failure.

From edge computing innovations to deeper integrations with SAP, Lenovo's datacenter roadmap aims to position the company as a major hyperscale contender.
- By John K. Waters
- 05/15/2019

If you've noticed some of your Windows 10 applications taking less and less screen real estate over time, you're not alone. Here are some workarounds.
Reimaging might be the easiest option but, as Brien explains, there are certain situations where that just won't work.

It's easy enough to tell if Office 365 is having performance issues (or is plain down). It's a litle harder to figure out whether the problem is with Microsoft or with you.

Microsoft's ongoing investments in SQL Server are bearing fruit. Here's a rundown of the biggest announcements for database professionals from this year's conference.
- By Joey D'Antoni
- 05/06/2019

A recent report suggests that Microsoft's own e-mail security protections have trouble differentiating between real and fraudulent messages from itself.
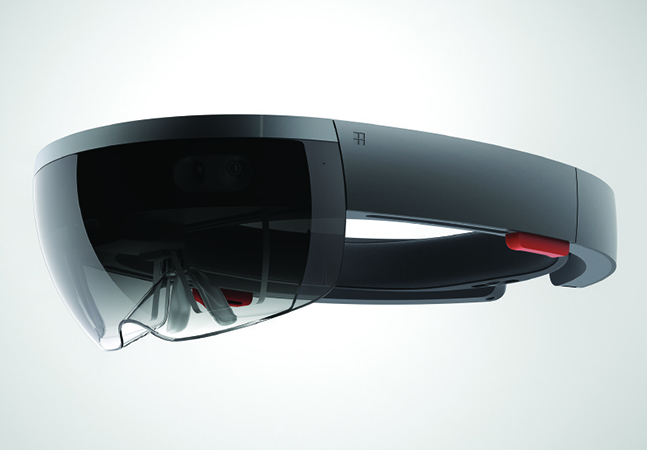
Attempts to pigeonhole Microsoft's mixed reality device into a specific use case -- whether it's work or play -- are missing the point, Brien argues.